Theme

Industry trends
5 min
Electric Vehicle Charging Stations – An Automotive Cyber Security Threat
Isolated, unmanned electric vehicle charging stations threaten vehicle cyber security. Integral data connectivity links user, vehicle and station opening new avenues of attack.
NNG
26 Aug, 2019
Editors Note: A version of this article was first published in Automotive World in May 2019. (Read the original here: https://www.automotiveworld.com/articles/electric-vehicle-charging-stations-a-new-automotive-cyber-security-threat/)
Electric Vehicle Charging Stations are a threat to vehicle cyber-security. Unmanned, out-of-the-way locations, and integral data connectivity linking user, vehicle, and station open a variety of avenues for attack.
Charging Stations Require Connectivity
As electric vehicles (EVs) become more common – and the number of charging stations to support them continues to increase – it becomes vital to consider what cyber-security risks this infrastructure creates and what steps can be taken to mitigate them.
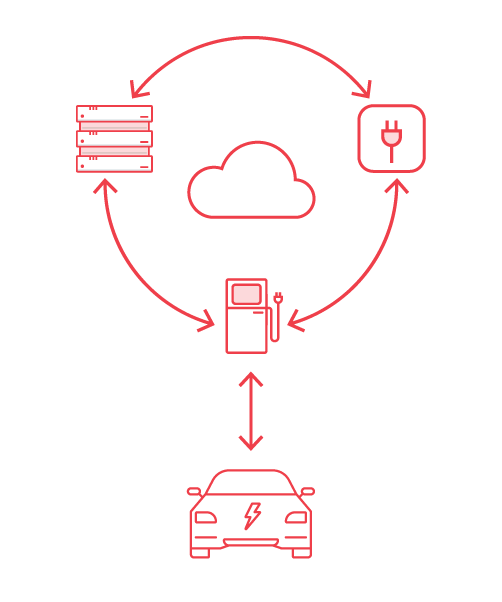
Charging stations require data connectivity to function. Not just for the purposes of sending charging and billing data from the station to the vendor’s servers, but also for communicating with the car. Users also typically manage their charging experience from a dedicated mobile app which contains payment and personal information. These apps, in turn, send and receive data to and from a vendor’s servers, and may communicate directly with the charging station via contactless payment methods.
Charging Stations are Vulnerable Physically and Remotely
EV charging stations, like their fossil-fuelled counterparts, are often located in out of the way places to allow for on- and off-the-road refuelling. However, unlike traditional fuel stations, most charging points are unmanned, leaving hackers with potentially unrestricted physical access.
This is bad for several reasons, not least of which is that with unfettered access a malicious actor could place malware or trojan software on the charging unit – allowing them to hack a vehicle (or device used for payment) when it connects to the charging station.
But we must also consider how the charging station connects to wider infrastructure. Vendor backend servers – which hold user profile and payment data – are vulnerable via their internet connection. They are often cloud-based and connect with the charging station as well as user apps. A poorly secured station could potentially offer unrestricted access to the whole network.
The Vehicle is Vulnerable
New EVs are commonly fitted with intelligent charging modules, which communicate charging data between the vehicle and the charging station. These systems help to streamline the charging process, but they also represent a direct line of access to the vehicle’s critical systems. Like any vulnerable electronic control unit (ECU), these modules are connected to the in-vehicle network (IVN), and as such offer a vector for determined hackers to abuse.

Electric Vehicle Charging Station Hacking
0:56
Protecting the in-vehicle network against hacks is the best defense against a rapidly evolving threat.
A Lack of Standardization
A lack of standard design and little consideration of cyber-security design principles during the early development of charging stations means that security levels vary across existing networks. While one station may be robust enough to protect against infiltration another may not.
Until regulation and standardisation limit the risks of plugging into a given station, it remains clear that vehicle manufacturers should focus on protecting the vehicle’s critical systems from attack. Either by creating a secure network architecture, securing the gateway between the vehicles charging module and critical IVNs or by protecting the IVN itself with robust intrusion detection and prevention systems.
Charging Stations are an Evolving Threat
The infrastructure and charging networks that are necessary to support EVs are unlikely to become robustly secure soon. There are just too many variables to consider, from different EV vendors and charging interfaces to the varied selection of charging station vendors themselves.
With no change to this situation in sight, it is vital to look at what it is possible to secure. Consider the charging station in your automotive cyber-security strategy. Consider the charging station to be another vector into the vehicle, and the intelligent charging module to be another vulnerable connected ECU. Look for ways to mitigate that threat.
Protection of critical in-vehicle networks is still the most key area to consider, whether this is through IVN protection, end-point or gateway intrusion detection and prevention systems.
If you would like to find out more about Arilou’s in-vehicle network cyber-security solutions. Please contact us.
Would you like to know more?
Get in touch to learn more about our latest products and services or company news